

The public cloud will confidently tell you that the data belongs to you. Legally, that is true. But there is a gap between data ownership and actual control over the infrastructure, and this gap easily accommodates jurisdictional risks, vendor lock-in, and an opaque shared responsibility model. Let’s break down where organizations lose visibility over their data and why data center colocation represents a strategic response for companies that do not want to merely rent control.
The answer to where control over data starts to fade is not found in a single point. It runs through the entire architecture, from the shared responsibility model and dependence on a specific ecosystem to the jurisdiction your data falls under. Let’s go through these layers one by one.
Do You Own Your Data or Just a Contract? The Difference Between Logical and Physical Ownership
Cloud providers state in their terms that the data remains the property of the customer. Formally, this is true. In practice, however, organizations hand over physical control of the infrastructure—servers, storage, and network components—to the provider. This is where the shared responsibility model comes into play. The provider ensures the security of the cloud infrastructure itself, while the customer is responsible for securing their data, applications, access policies, and configurations.
It sounds logical, but reality tells a different story. According to industry analysts, most cloud security incidents originate on the customer side, typically due to misconfigurations or insufficient access management. And the issue is not just about who is responsible for what. The customer does not have direct access to the physical layer of the infrastructure and cannot fully verify how the provider handles their environment at the hardware level. As a result, data ownership remains more of a legal concept than an operational reality.
Vendor Lock-In and Hidden Dependency – Why Data Center Colocation Changes the Game
The public cloud offers rapid scalability and operational convenience. But this flexibility comes at the cost of increasing dependence on a single ecosystem. Proprietary tools, formats, and APIs create an environment that is difficult and expensive to leave. Vendor lock-in is not just a technical issue; it weakens negotiating power, complicates migration, and in extreme cases dictates the conditions under which a company operates its own data.
Data center colocation reverses this model. Organizations own their hardware, control software configurations, and decide on the network architecture, all within a professional data center environment that provides power, cooling, physical security, and connectivity. A carrier-neutral setup also enables freedom of choice when it comes to operators and cloud partners, without one-sided dependence on a single provider. Providers such as ttc-teleport.cz/en/ build this approach on decades of experience and a transparent model where customers design their services themselves and pay only for what they actually use.
Data Sovereignty and the Jurisdiction Roulette – Who Decides About Your Data?
When organizations place data in the public cloud, they automatically subject it to the jurisdiction under which the provider operates. For US hyperscalers, this means exposure to the US CLOUD Act, a federal law that allows US authorities to request data from American providers regardless of where the servers are physically located. In 2025, Microsoft openly admitted that it cannot guarantee data sovereignty for European customers. This is not a theoretical risk; it is an operational reality that every company handling sensitive data must address.
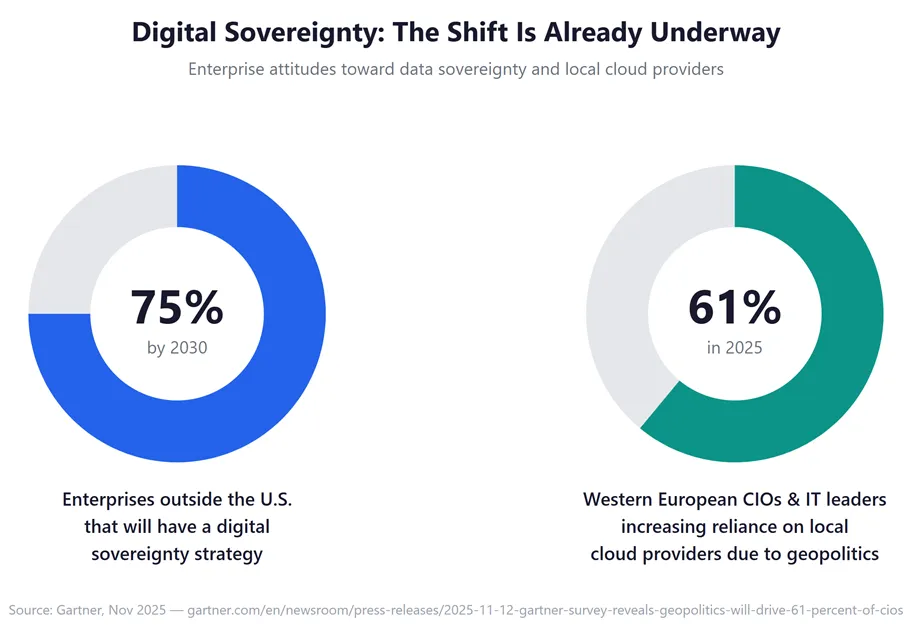
Regulatory pressure is increasing on both sides of the Atlantic. The European NIS2 directive expands cybersecurity obligations to additional sectors, including data centers, while the DORA regulation tightens requirements for ICT resilience in the financial sector. Gartner predicts that by 2030, more than 75% of enterprises outside the US will have their own digital sovereignty strategy. For organizations in finance, healthcare, or industry, this is not a choice; it is a condition for operating.
Physical Control as the Foundation of Security – What Data Center Colocation Offers Beyond
Cloud security risks do not stem from hyperscalers doing a poor job. They stem from the fact that the customer loses direct contact with the physical layer. In a colocation model, the organization decides on every detail, from hardware selection and network topology to access protocols. The data center provides a secure perimeter, redundant power, and connectivity, while the customer retains full control over what happens inside their rack.
This architecture also simplifies audit processes and compliance verification. Certifications such as ISO 27001 or SOC 2 on the data center side complement the organization’s own security policies, creating a transparent layered model in which each party has clearly defined responsibilities. Unlike the shared responsibility model in the cloud, there are no gray areas here.
A Decision That Won’t Wait
The gap between data ownership and actual control will not close on its own. Regulations are tightening, geopolitical tensions are rising, and dependence on a single ecosystem is deepening with each passing month. Data center colocation is not a step back into the past; it is a strategic response for organizations that refuse to trade control for convenience.






Leave a Reply